Nobody is immune to hacking and cyber attacks. Almost all major hotel chains and tech companies have been hacked in recent years. It’s not just the hotel industry either - some of the biggest data breaches in history have been inflicted on the most advanced tech companies in the world like Adobe, LinkedIn and eBay.
As hoteliers we don’t have time to take advanced online cybersecurity courses or go back to college for a masters in geopolitics. At the same time, we’re all increasingly afraid that our property is going to be featured in the next front page newspaper headline about hackers stealing data from the hotel industry.
A guest data breach opens us to public scrutiny, damages our reputation and exposes our businesses to massive financial liability.
While it’s impossible to outright prevent cyber attacks in today’s complex digital businesses environment, we’re all responsible for protecting guests and mitigating risks to the best of our abilities. In order to help you protect your customers and your hotel business you’ll need to first understand a bit about the recent history of hacking.
This article will inform you on the latest data security trends. It will then apply these learnings to hotel technology decision making. Specifically we’re going to focus on how to mitigate the risks associated with vendor selection through geographic screening, financial diligence and IT architecture.
Data Sovereignty and Cybersecurity
Data sovereignty refers to the rights and storage of company and customer data based on geography. The main purpose of data sovereignty laws is to secure data and ensure the privacy of populations from foreign threats. Data sovereignty began to popularize around the time that GDPR laws went into effect. The data privacy movement has largely been spearheaded by Europe with the United States and Canada as fast followers.
Unsurprisingly, the lion’s share of data sovereignty debates have occurred between Western countries (U.S. & E.U.) and China. China’s rapid rise to power has come with many reforms but the country still faces significant stigmas associated with its approach to data privacy and intelligence gathering.
China has a different vision from the West (and many in the East) for the future of the internet:
“China has pushed through dozens of regulations and technical standards that, in conjunction, bolster the government’s control of and visibility into the entire internet ecosystem, from the infrastructure that undergirds the internet, to the flow of data, to the dissemination of information online, to the make-up of the software and hardware that form the basis of everything from e-commerce to industrial control systems.” ~ The Atlantic
So what does Xi Jinping and the PRC’s vision for the future of cybersecurity and data sovereignty have to do with your hotel business? In short, a lot.
Data Sovereignty and Hotel Tech Vendor Selection
Back in March of 2020 the hotel tech world was shocked when American President Donald Trump took action to block Shiji’s acquisition of U.S. property management system StayNTouch. Some conspiracy theorists attempted to draw connections to Trump’s relationship with Oracle founder Larry Ellison in the wake of Shiji cancelling it’s longstanding reseller agreement with the firm.
These theories fail to put the dispute into the larger context of Chinese data security issues in recent decades. Trump’s blockage of Shiji’s deal is hardly the first straw drawn in the cyber dispute between the West and China. Before we assess the potential and perceived risks associated with U.S. and European hotels purchasing Chinese technology, let’s look at the history of data surveillance.
Understanding Risk in the Context of Huawei
China is hardly the first government to develop a global monitoring system. Back in the 1960s the American government began collaborating with the U.K. to develop a global system of satellites and software backdoors that would later expand to other allies such as Canada, Australia and New Zealand (Five Eyes Intelligence Alliance). Global telecom powerhouse Huawei is widely regarded as China’s solution to the West’s multi-decade head start on surveillance technology.
“Huawei’s corporate strategy – which is to say, the strategy of China’s intelligence services – is to grant massive discounts on the installation of a network’s less critical bits on the condition that Huawei can also install and maintain the cores,” says Peter Ziehan, a leading geopolitics strategist.
In March of 2019, the Five Eyes alliance officially blocked Huawei’s ability to deploy 5G technology into its member states. Additionally, the US government banned US firms from selling components to the firm. For critics who claim that Trump’s reaction to the StayNTouch acquisition is a blunt overreaction, the Huawei response is orders of magnitude more severe.
So why was this action taken against Huawei? “Huawei would have no choice but to hand over network data to the Chinese government if Beijing asked for it, because of espionage and national security laws in the country,” experts told CNBC.
A Stark Contrast with U.S. and European Tech
There are signs of reform in China coming from the corporate sector but these signs are early at best. Alibaba and Tencent have recently attempted to refuse sending data to Beijing (mostly unsuccessfully). Notably, Alibaba is a minority investor in Shiji after making a $486M investment in the firm back in 2014.
Similarly, WeChat made a decision not to store chat logs on its platform. Many believe this was to remove the responsibility of sending on demand data to Beijing. Others are skeptical of whether the firm is being honest in it’s claim that it doesn’t store chat data.
Despite these small but important reforms, the paradigm within western democratic data sovereignty lies in stark contrast to that seen in China where U.S. and European companies are in constant litigation around user data with governments and visa versa - a testament to the checks and balances that preserve the rights and privacy of consumers. These checks and balances are far from perfect, but they lay the groundwork for progress.
In 2015, Apple famously declined the U.S. government’s request to unlock a criminal’s iPhone citing its unflinching focus on security and user privacy. A letter from Apple to iPhone customers demonstrates just how difficult it is for U.S. authorities to violate consumer privacy:
“The implications of the government’s demands are chilling. If the government can use the All Writs Act to make it easier to unlock your iPhone, it would have the power to reach into anyone’s device to capture their data. The government could extend this breach of privacy and demand that Apple build surveillance software to intercept your messages, access your health records or financial data, track your location, or even access your phone’s microphone or camera without your knowledge.” Apple Customer Letter
Not only do U.S. and European companies have the ability to substantially fight their government in the interests of consumer privacy, but Western governments have demonstrated an interest in regulating the same for their corporate counterparts. This fact has been highlighted numerous times in recent years. Perhaps the highest profile case relates to U.S. federal regulators mounting a legal offensive against Facebook for it’s handling of customer data in the context of Cambridge Analytica. EU regulators are perhaps even more aggressive in their protection of consumer data as evidenced by a lawsuit against Google resulting in a $57M fine.
The important takeaway here is that U.S. and European companies can publicly (and aggressively) fight the government and visa versa. In China, that still seems to not be the case and that likely poses a material risk to any U.S. or European hotel property that chooses to adopt Chinese technology.
It’s Just Business
In our increasingly globalized economies xenophobia is dangerous and counterproductive. The arguments being made here are far from that - these are important business considerations. China has a vested interest in its new kind of patrolled internet and despite activists' criticism, those interests are well founded based on its desire to maintain domestic security and prevent internal social unrest.
There are no “good guys” and “bad guys” in this debate, it’s merely a political and strategic dance between different interests and cultures. Having said that, China’s national interests and world views are in stark conflict with those of the democratic Western countries in Europe and North America meaning that private businesses who consider adopting Chinese technology need to consider the implications of that conflict. So what are the implications for private businesses like your hotel?
As experienced hoteliers know, corporate meeting planners from major clients like Google manage a close knit group of hotel partners that are certified to host high profile meetings. These partners are closely vetted based on security protocols. Oftentimes these hotels need to enter corporate code names into the PMS upon booking in order to maintain confidentiality and mitigate any potential risks.
So if corporate groups like Google and Amazon require secure hotel meeting environments it’s no shock that the U.S. government demands the same. The U.S. government is a major corporate group segment for hotels. Given the steps taken by corporations like Google and Amazon to ensure secure meetings it’s no wonder that the Federal government doesn’t want China to have access to government worker data and government meeting information. Additionally, China has a history of being linked to hotel industry hacking.
In February of 2020 the United States Department of Justice formally charged four members of the Chinese military in connection with the 2017 Equifax hack leaking identifying information about millions of people in the U.S. “The Equifax attack was explicitly linked to the Marriott and OPM breaches as part of the same larger operation. This was an extremely rare move — the U.S. rarely files criminal charges against foreign intelligence officers in order to avoid retaliation against American operatives — that underscored how seriously the U.S. government took the attack” writes the New York Times.
Additionally there is evidence connecting China directly to the massive Starwood/Marriott hack, “The cyberattack on the Marriott hotel chain that collected personal details of roughly 500 million guests was part of a Chinese intelligence-gathering effort that also hacked health insurers and the security clearance files of millions more Americans, according to two people briefed on the investigation.” Security experts point out the fact that Starwood’s data leak was never released online for sale on the dark web. They assert that if the hackers didn’t do this for the money, it’s highly probable that this was related to an intelligence gathering exploit.
How is Your Hotel Affected?
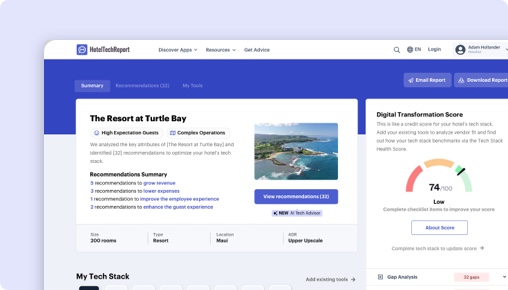
There are many technical ways to mitigate these risks such as penetration testing, hiring a cyber security audit firm, securing WiFi networks and more. The single most important thing that any hotel can do to mitigate cyber risk is to be diligent in hotel technology vendor selection.
As we saw in the case of Starwood’s hack, Marriott ended up taking responsibility despite not being the responsible party at the time of the breach. The same goes for your hotel. Every manager and IT leader needs to understand their technology architecture, vulnerabilities and steps being taken to protect their guests. Technology firms spend millions of dollars on engineering to ensure this security but it’s on hotel tech buyers to ensure that they’re asking the right questions and selecting the right vendors.
Every hotelier needs to understand the data sovereignty of their systems. It’s important to consider the risks of storing your guest data in China or other regions of the world that might be vulnerable to leakage, hacking or straight up confiscation by local governments.
Another important facet to consider is the financial viability of your technology partners. Businesses that are cash strapped or struggling often aren’t able to invest to the same level in cyber security and innovation which poses a risk. SaaS stands for “software as a service” and while you might be “buying”tech today, the shrewdest buyers understand that they are buying into the future of that business including their product roadmap and investments in critical innovation to remain competitive. Just last year, Drury Hotels was forced to notify guests of a security incident that occured on an undisclosed third party technology service provider involving information related to online booking sites.
The best way to ensure that your hotel group does not become the next Drury Hotels is to perform extensive diligence on your vendors. Where are they located? Where does data get stored? Who has the rights to that data? How much have they invested in cyber security? What steps and protocols exist to ensure that your hotel’s data (especially sensitive guest data) is kept from malicious cyber attacks?